Confidential PDF indexes are crucial for organizing sensitive data‚ mirroring forum discussions about information security and document protection‚ as seen on platforms like Index Fórum.
What are Confidential PDFs?
Confidential PDFs encompass documents containing sensitive information requiring restricted access‚ mirroring discussions found on platforms like Index Fórum regarding data security. These files often include personal data‚ financial records‚ or proprietary business information. They necessitate robust protection measures to prevent unauthorized viewing‚ modification‚ or distribution.
The inherent nature of PDFs – their ability to embed various data types‚ including images and text – makes them a common target for malicious actors. As highlighted in research analyzing encrypted PDFs‚ they are frequently used to store and transmit sensitive content. Therefore‚ understanding the characteristics of confidential PDFs is the first step towards implementing effective security protocols‚ ensuring data integrity and compliance with regulations like GDPR and CCPA.
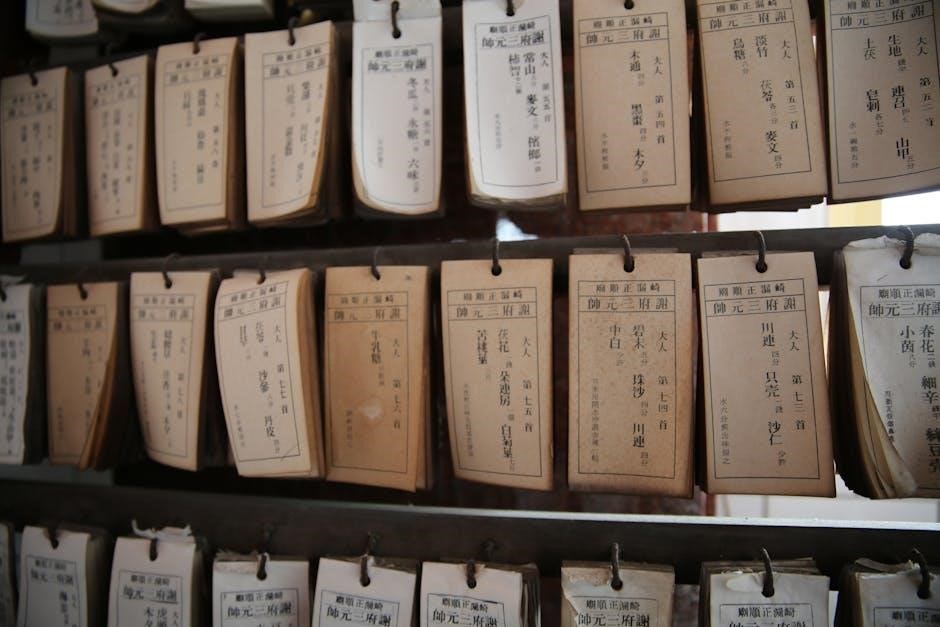
The Importance of Indexing Confidential Documents
Indexing confidential documents‚ including PDFs‚ is paramount for efficient retrieval and management‚ echoing the organizational needs discussed within online forums like Index Fórum. A well-structured index facilitates quick access to critical information‚ streamlining workflows and reducing search times. However‚ the index itself becomes a valuable target; securing it is as vital as protecting the documents it references.
Without a secure index‚ locating specific confidential PDFs can be cumbersome and time-consuming. Moreover‚ a compromised index could expose the existence and location of sensitive data‚ creating significant security vulnerabilities. Effective indexing‚ coupled with robust security measures‚ ensures both accessibility and confidentiality‚ aligning with data privacy regulations and corporate security policies.
Risks Associated with Unsecured PDF Indexes
Unsecured PDF indexes present substantial risks‚ potentially revealing the presence and location of confidential information – a concern mirrored in online security discussions like those found on Index Fórum. A compromised index acts as a roadmap for attackers‚ enabling targeted breaches and data exfiltration. This vulnerability extends beyond the documents themselves‚ impacting compliance with regulations like GDPR and CCPA.
Without proper access controls and encryption‚ an unsecured index can be exploited through phishing attacks or social engineering‚ as highlighted in security analyses. Malware embedded within the index or linked documents further amplifies the threat. Regularly auditing and securing the index is crucial to mitigate these risks and maintain data confidentiality.

Understanding PDF Security Features
PDF security features‚ like encryption and digital signatures‚ are vital for protecting confidential indexes‚ mirroring concerns discussed in online security forums and research.
Password Protection and Encryption
Password protection forms a foundational layer of security for confidential PDF indexes‚ controlling access and preventing unauthorized viewing. However‚ passwords alone are often insufficient; robust encryption algorithms are essential. These algorithms‚ such as AES‚ scramble the PDF’s content‚ rendering it unreadable without the correct decryption key.
The strength of encryption directly impacts the index’s security. Weak or outdated encryption can be easily bypassed. Modern PDF security standards emphasize strong encryption alongside password protection. Discussions on platforms like Index Fórum highlight the importance of regularly updating security measures to counter evolving threats. Properly implemented encryption ensures that even if a PDF index falls into the wrong hands‚ the contained information remains confidential and protected from exploitation‚ mirroring concerns about data breaches.
Digital Signatures for Authenticity
Digital signatures are paramount for verifying the authenticity and integrity of confidential PDF indexes. Unlike passwords‚ which confirm who is accessing the document‚ signatures confirm that the document hasn’t been altered since it was signed and identify the signer. This is crucial when dealing with sensitive information‚ as highlighted in discussions surrounding information security‚ similar to those found on platforms like Index Fórum.
A digital signature uses cryptographic techniques to bind the signer’s identity to the PDF. Any modification to the index after signing invalidates the signature‚ immediately alerting users to potential tampering. This provides a non-repudiation feature‚ meaning the signer cannot deny having signed the document. Ensuring authenticity is vital for legal compliance and maintaining trust in confidential data‚ mirroring concerns about document verification.
Permissions and Restrictions
Permissions and restrictions within confidential PDF indexes are essential for controlling access and preventing unauthorized actions. These features‚ often discussed alongside broader security concerns like those found on forums such as Index Fórum‚ allow administrators to define precisely what users can do with a document. Restrictions can include disabling printing‚ copying‚ or modification‚ safeguarding sensitive information from exposure.
Granular control extends to specifying permitted actions – for example‚ allowing viewing but prohibiting editing. This layered approach to security is vital when handling confidential data. Properly configured permissions ensure that only authorized personnel can access and manipulate the index‚ mitigating risks associated with data breaches and maintaining compliance with data privacy regulations. Careful implementation is key to a robust security posture.
Creating a Secure PDF Index
Secure PDF index creation involves meticulous metadata management‚ strong encryption‚ and robust access controls‚ mirroring discussions on platforms like Index Fórum.
Metadata Management for Confidentiality
Effective metadata management is paramount when indexing confidential PDFs‚ acting as a first line of defense against unauthorized access. Carefully consider what information is embedded within the document’s properties – author‚ title‚ keywords‚ and subject – as this data can be exploited. Remove or redact any sensitive details not essential for indexing or retrieval.
Implement a consistent metadata schema across all confidential documents to facilitate accurate searching and filtering while minimizing exposure. Utilize custom metadata fields to categorize documents based on sensitivity levels‚ departments‚ or projects. Regularly review and update metadata to ensure its accuracy and relevance‚ reflecting changes in document status or classification. This practice‚ akin to maintaining organized forum threads on platforms like Index Fórum‚ ensures efficient and secure information handling.
Using Strong Encryption Algorithms
Employing robust encryption algorithms is fundamental to securing confidential PDF indexes‚ safeguarding data against unauthorized decryption. AES (Advanced Encryption Standard) with a 256-bit key is currently considered the gold standard‚ offering a high level of security. Avoid older or weaker algorithms like DES or RC4‚ which are vulnerable to attacks.
When creating the PDF index‚ ensure the encryption settings are correctly applied to both the document content and any associated metadata. Regularly evaluate and update encryption standards to stay ahead of evolving threats‚ mirroring the constant vigilance required in online security discussions‚ such as those found on platforms like Index Fórum. Proper implementation‚ alongside strong passwords‚ forms a critical barrier against data breaches.
Implementing Access Controls
Robust access controls are paramount when managing confidential PDF indexes‚ limiting exposure to authorized personnel only. This involves defining granular permissions – read‚ write‚ print‚ and copy – based on user roles and responsibilities. Utilize password protection in conjunction with these controls‚ enforcing strong password policies and multi-factor authentication where feasible.
Centralized management of access rights simplifies administration and auditing. Regularly review and update permissions to reflect changes in personnel or security requirements‚ mirroring the dynamic nature of online forum discussions regarding data security‚ like those on Index Fórum. Implementing these controls minimizes the risk of unauthorized access and data breaches‚ protecting sensitive information within the index.

Tools for Secure PDF Indexing
Adobe Acrobat and third-party software offer robust security features for PDF indexing‚ including encryption and access controls‚ vital for protecting confidential data.
Adobe Acrobat Security Features
Adobe Acrobat provides a comprehensive suite of tools for securing PDF indexes containing confidential information. Password protection and encryption are fundamental‚ safeguarding documents from unauthorized access. Acrobat supports various encryption algorithms‚ ensuring robust data confidentiality.
Digital signatures verify document authenticity and integrity‚ crucial for legal and compliance requirements. Permissions and restrictions allow granular control over what recipients can do with the PDF – viewing‚ printing‚ editing‚ or copying.
Furthermore‚ Acrobat’s redaction tools permanently remove sensitive information from the index and document content. These features‚ combined with regular security updates‚ make Acrobat a powerful solution for managing and protecting confidential PDF indexes‚ addressing concerns highlighted in discussions about data security.
Third-Party PDF Security Software
Beyond Adobe Acrobat‚ numerous third-party solutions enhance the security of confidential PDF indexes. These often provide advanced features like data loss prevention (DLP) integration and more sophisticated encryption methods. Some specialize in rights management‚ controlling access and usage even after the PDF leaves the organization.
Several vendors offer tools focused on identifying and neutralizing potential threats embedded within PDF files‚ addressing concerns about malware and phishing attacks. These solutions frequently include features for auditing access and tracking document activity.
Choosing the right software depends on specific security needs and compliance requirements‚ offering alternatives to built-in features for robust protection of sensitive PDF indexes.
Open-Source Solutions for PDF Security
For organizations prioritizing cost-effectiveness and customization‚ open-source tools offer viable options for securing confidential PDF indexes. These solutions often provide core security functionalities like encryption and digital signature support‚ allowing for greater control over the security infrastructure.
While requiring more technical expertise for implementation and maintenance‚ open-source alternatives can be audited and modified to meet specific security policies. Several libraries and frameworks facilitate PDF manipulation and security features‚ enabling developers to build custom solutions.
However‚ reliance on community support and potential licensing considerations should be carefully evaluated when choosing open-source PDF security tools.

Best Practices for Handling Confidential PDF Indexes
Prioritize data classification‚ secure storage‚ and regular security audits‚ mirroring forum discussions on protecting sensitive information within PDF indexes and related documents.
Data Classification and Labeling
Implementing a robust data classification system is paramount when dealing with confidential PDF indexes. This involves categorizing documents based on sensitivity – for example‚ ‘Restricted‚’ ‘Confidential‚’ or ‘Public’ – mirroring the need for responsible content handling discussed on platforms like Index Fórum.
Clear labeling‚ both within the PDF metadata and through visual markings (watermarks‚ headers/footers)‚ ensures proper handling throughout the document lifecycle. Consistent labeling aids in enforcing access controls and supports compliance with regulations like GDPR and CCPA‚ as highlighted in discussions about enterprise data protection.
Accurate classification minimizes the risk of unauthorized access and accidental disclosure‚ aligning with security models for indexes and the broader need to safeguard sensitive information‚ as explored in research on encrypted PDF security.
Secure Storage and Transmission
Protecting confidential PDF indexes necessitates secure storage solutions‚ employing encryption at rest to prevent unauthorized access even in the event of a breach. This aligns with the broader security concerns discussed on platforms like Index Fórum regarding data protection within enterprises.
Transmission of these indexes requires equally robust measures‚ such as TLS/SSL encryption for data in transit. Utilizing secure file transfer protocols (SFTP) and avoiding email attachments for sensitive documents are crucial best practices.
Regularly auditing storage and transmission methods ensures ongoing security‚ mirroring the need for vigilance against phishing and malware embedded in PDFs‚ as highlighted in security research and discussions about protecting confidential images within PDF wrappers.
Regular Security Audits
Consistent security audits are paramount for maintaining the integrity of confidential PDF indexes‚ mirroring the proactive security discussions found on platforms like Index Fórum. These audits should encompass a comprehensive review of access controls‚ encryption algorithms‚ and data storage practices.
Vulnerability assessments and penetration testing can identify weaknesses in the system‚ proactively addressing potential exploits before they are leveraged. This aligns with the need to counter phishing attacks and social engineering tactics targeting PDF credentials.
Audit logs must be meticulously reviewed to detect any unauthorized access or modification attempts. Regular updates to security software and adherence to data privacy regulations (GDPR‚ CCPA) are also essential components of a robust security posture.

Addressing Common Security Vulnerabilities
PDF index security requires vigilance against phishing‚ social engineering‚ and malware‚ mirroring concerns discussed on platforms like Index Fórum regarding online threats.
Phishing Attacks Targeting PDF Credentials
Phishing campaigns frequently leverage PDF documents to steal user credentials. Attackers craft seemingly legitimate PDFs‚ often mimicking official communications‚ that prompt users to enter usernames and passwords to view the content or access an “indexed” resource. These PDFs may contain embedded forms or redirect to fake login pages designed to harvest sensitive information.
The discussions on platforms like Index Fórum highlight the importance of user awareness regarding suspicious emails and attachments. Users should carefully examine the sender’s address‚ look for grammatical errors‚ and avoid clicking links or entering credentials in PDFs from untrusted sources. Employing multi-factor authentication adds an extra layer of security‚ mitigating the impact of compromised credentials obtained through phishing attacks targeting PDF indexes.
Social Engineering and PDF Exploits
Social engineering tactics often accompany PDF-based attacks‚ exploiting human psychology to gain access to confidential information linked to PDF indexes. Attackers might impersonate trusted entities‚ leveraging urgency or authority to convince users to open malicious PDFs or divulge sensitive data. These PDFs can contain hidden exploits that‚ when triggered‚ compromise the user’s system.
Discussions on forums like Index Fórum emphasize the need for skepticism and verification. Users should independently confirm requests‚ especially those involving sensitive documents or credentials. Regularly updating PDF readers and operating systems patches known vulnerabilities‚ reducing the risk of successful exploits. Training employees to recognize and report social engineering attempts is crucial for protecting confidential PDF indexes and associated data.
Malware Embedded in PDF Files
PDF files can serve as vectors for delivering malware‚ posing a significant threat to confidential PDF indexes and the data they reference. Attackers embed malicious code within PDF structures‚ exploiting vulnerabilities in PDF readers to execute harmful payloads upon opening. This malware can range from ransomware and Trojans to spyware‚ compromising systems and stealing sensitive information.
The Index Fórum discussions highlight the importance of robust endpoint security solutions‚ including antivirus software and intrusion detection systems. Scanning PDFs before opening‚ particularly those from untrusted sources‚ is crucial. Employing sandboxing technology isolates PDF execution‚ preventing malware from impacting the core system. Regularly updating security software and practicing safe browsing habits are essential defenses against PDF-borne malware targeting confidential indexes.
Legal and Compliance Considerations
Confidential PDF indexes must adhere to data privacy regulations like GDPR and CCPA‚ alongside industry standards such as HIPAA and PCI DSS‚ ensuring legal compliance.
Data Privacy Regulations (GDPR‚ CCPA)
Confidential PDF indexes fall under stringent data privacy regulations like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). These laws mandate organizations to protect personal data within indexed documents‚ requiring explicit consent for data processing and secure storage practices.
Compliance involves implementing robust access controls‚ data minimization techniques‚ and transparent data handling policies. Organizations must demonstrate accountability for data protection‚ including providing individuals with rights to access‚ rectify‚ and erase their personal information contained within the indexed PDFs. Failure to comply can result in substantial fines and reputational damage‚ emphasizing the critical need for secure PDF indexing practices aligned with these regulations.
Industry-Specific Compliance Standards (HIPAA‚ PCI DSS)
Confidential PDF indexes handling sensitive information are subject to industry-specific compliance standards like HIPAA (healthcare) and PCI DSS (payment card industry). HIPAA mandates strict privacy and security rules for protected health information within indexed documents‚ demanding secure access controls and audit trails.
PCI DSS requires secure handling of cardholder data‚ necessitating encryption and robust security measures for any PDF indexes containing payment information. Compliance involves regular security assessments‚ vulnerability scanning‚ and adherence to specific technical and operational requirements. Organizations must demonstrate ongoing compliance to maintain trust and avoid penalties‚ highlighting the importance of tailored security protocols for confidential PDF indexes within regulated industries.
Document Retention Policies
Confidential PDF indexes necessitate well-defined document retention policies to manage data lifecycle and comply with legal requirements. These policies dictate how long indexed PDFs are stored‚ archived‚ and ultimately disposed of‚ balancing business needs with regulatory obligations.
Retention schedules should categorize documents based on sensitivity and legal hold requirements‚ ensuring appropriate handling of confidential information. Secure deletion methods are crucial to prevent data breaches‚ while archiving strategies must maintain index integrity and accessibility. Regular review and updates to retention policies are essential‚ reflecting evolving regulations and organizational needs‚ safeguarding confidential PDF indexes throughout their lifecycle.

Future Trends in PDF Security
PDF security evolves with AI-powered threat detection‚ blockchain verification‚ and advanced encryption‚ enhancing confidential PDF index protection against emerging vulnerabilities.
Advanced Encryption Techniques
Advanced encryption techniques are becoming paramount for securing confidential PDF indexes‚ moving beyond traditional methods. Research highlights the need for robust protection‚ especially when dealing with sensitive images embedded within PDF files. Future developments will likely focus on algorithms offering greater key lengths and resistance to brute-force attacks.
Homomorphic encryption‚ allowing computations on encrypted data‚ presents a promising avenue. This minimizes the need to decrypt information for processing‚ reducing exposure. Furthermore‚ quantum-resistant cryptography is gaining traction‚ preparing for a future where current encryption standards may be compromised. These techniques‚ coupled with secure indexing methods‚ will be vital for maintaining data confidentiality and integrity in the face of evolving threats‚ mirroring concerns discussed in online security forums.
Blockchain Integration for Document Verification
Blockchain integration offers a revolutionary approach to verifying the authenticity and integrity of confidential PDF indexes. By creating a tamper-proof record of document hashes on a distributed ledger‚ any unauthorized modification becomes immediately detectable. This addresses concerns about data manipulation‚ echoing discussions on online forums regarding document security.
Each PDF index entry can be linked to a unique blockchain transaction‚ providing a clear audit trail. Smart contracts can automate access control and enforce permissions‚ enhancing security. While still emerging‚ this technology promises a higher level of trust and accountability‚ particularly crucial for highly sensitive information. This method complements existing encryption techniques‚ creating a multi-layered defense against breaches and ensuring data provenance.
AI-Powered Threat Detection
AI-powered threat detection is becoming vital for safeguarding confidential PDF indexes against evolving cyber threats‚ mirroring concerns discussed in online security forums. Machine learning algorithms can analyze user behavior‚ identifying anomalies that suggest malicious activity‚ like unauthorized access attempts or suspicious data exports.
These systems can detect phishing attacks targeting PDF credentials and recognize malware embedded within documents‚ proactively mitigating risks. AI can also classify documents based on sensitivity‚ automatically applying appropriate security measures. This intelligent approach enhances traditional security protocols‚ offering a dynamic defense against sophisticated attacks and ensuring the ongoing protection of sensitive information within the index.
